What Meta Just Announced
Meta announced in March 2026 that end-to-end encryption support for Instagram direct messages would be discontinued. The change takes effect May 8, 2026.
Importantly, this affects only the opt-in encrypted DM feature. Most Instagram users never enabled or even knew about E2EE—it was a hidden, difficult-to-find setting that required deliberate activation. The vast majority of Instagram conversations were never encrypted to begin with. This change removes the option for those who had discovered and chosen to use it.
Who's affected: All 2 billion Instagram users. However, most never used the optional encrypted DM feature.
What's being removed: The optional end-to-end encryption that allowed users to manually enable encrypted DMs in Instagram's messaging interface—a feature less than 5% of users had ever activated.
Implementation date: May 8, 2026 (announced in March, several months notice).
Meta's official statement emphasized that the removal is part of simplifying their messaging infrastructure and improving user adoption of their unified messaging system across Facebook, Instagram, and WhatsApp.
Users who want to preserve their existing encrypted messages should download their Instagram data before May 8. After the cutoff date, Meta will not maintain encryption support for DMs, meaning existing encrypted conversations may not be recoverable in encrypted form.
Why Meta Is Removing Encryption
Meta's stated reason: Low adoption. According to Meta's internal research, less than 5% of Instagram users had enabled encrypted DMs, making the feature a maintenance burden for relatively little user benefit.
Behind the technical reasoning lies a business strategy. Encrypted messaging limits Meta's ability to analyze content, detect patterns, and serve targeted advertising based on message data. While Meta frames encryption removal as a simplification effort, privacy advocates argue it's actually about gaining access to messaging data that was previously off-limits.
Meta's official perspective: DMs will still be "secure" through other security measures and their infrastructure protection, even without end-to-end encryption.
Privacy advocates' perspective: Without encryption, security depends entirely on Meta's internal controls, not on technical impossibility. If Meta is breached, all DM content becomes exposed.
The Take It Down Act Connection
There's another critical reason for the timing. The US Take It Down Act takes effect May 19, 2026—just 11 days after Meta's encryption cutoff. This law requires platforms to implement "reasonable measures" to detect and remove nonconsensual intimate images. Compliance with E2EE would be nearly impossible; platforms cannot detect illegal content if messages are encrypted. The timing is not coincidental. By removing encryption before the law takes effect, Meta ensures they can automatically scan, detect, and flag illegal content. While this addresses a real problem (nonconsensual imagery), it also removes a privacy feature that protected all users. Meta's "simplification" narrative conveniently omits this regulatory pressure.
Undermining the Simplification Argument
Interestingly, Meta's claim that encryption removal is about "simplification" doesn't hold up across their ecosystem. WhatsApp and Messenger both maintain end-to-end encryption as core features. If encryption was truly a burden on Meta's infrastructure, these platforms would also remove it. Instead, they've invested heavily in encryption technology. This suggests the encryption removal from Instagram is not about simplification, but about data access—Instagram is Meta's most ad-dependent platform, making unencrypted message data particularly valuable for behavioral targeting.
WhatsApp and Facebook Messenger maintain end-to-end encryption despite being owned by Meta. If simplification were the real goal, Meta would remove encryption from these platforms too.
Understanding Encryption in Instagram DMs (And Why It Mattered)
Before diving into impact, it helps to understand what end-to-end encryption actually did.
What it was: A security feature that scrambled your Instagram DM content so that only you and the recipient could read it. Not even Instagram's servers could read the encrypted message content.
How it worked: When you enabled encrypted DMs, Instagram used mathematical algorithms to turn your plain-text message into scrambled code. Only the recipient's device held the "key" to unscramble it. Instagram's servers stored the scrambled version, not the readable version.
What it protected: The actual content of your messages. If someone intercepted a message in transit or if Instagram's database was breached, the message would be unreadable without the decryption key.
What it didn't protect: Metadata. Encryption doesn't hide who you messaged, when you messaged them, or how often you communicate. That information was always visible to Instagram and remains visible.
This is an important distinction. Encryption makes your conversations private. Metadata analysis lets Meta know who your close contacts are, how often you talk, and when conversations happen. Meta can build a detailed social graph from metadata alone, even without reading your messages.
What This Change Means for Your Privacy
Starting May 8, Instagram direct messages are no longer encrypted by default. Here's the practical impact:
Meta can now read all your Instagram DMs. Not by breaking encryption or hacking—simply because DMs are now stored in readable format on Meta's servers. Any administrator with access, any internal process scanning messages, and any data-sharing partner with proper authorization can potentially read your DMs.
Data retention: Instagram stores DM data for extended periods (Meta's retention policy is not transparent to users). This means years of your message history could be archived and accessible.
Who can access your DMs:
- Meta employees (thousands of people)
- Government agencies with proper legal warrants
- Hackers if Instagram's systems are breached
- Data-sharing partners if Meta agrees to share
- Internal automated systems analyzing content for ads and behavior profiling
Before vs. After Privacy:
Before May 8: Conversations using encrypted DMs = unreadable to Meta, visible only to you and recipient.
After (May 8+): All conversations = readable by Meta, stored indefinitely, potentially used for ad targeting and behavioral analysis.
Real-world implications: Meta can now use DM content to:
- Build more detailed behavioral profiles (hobbies, interests, political views, relationships)
- Target ads with even greater precision
- Detect patterns and predict user behavior
- Share anonymized insights with data partners
This isn't theoretical. Meta has a documented history of using message data when available. Notably, WhatsApp and Facebook Messenger maintain end-to-end encryption despite being owned by Meta—a choice that directly contradicts the "simplification" narrative used to explain Instagram's encryption removal. If simplification were the real goal, Meta would also remove encryption from WhatsApp and Messenger. The fact that they maintain encryption on those platforms suggests the Instagram decision is driven by other factors (data analysis, regulatory compliance, ad targeting) rather than technical simplification.
Honest assessment: This doesn't mean Meta will publish your DMs or use them maliciously. It means your private conversations become part of your behavioral profile, feeding Meta's advertising and AI training systems.
What You Should Do Right Now (Action Steps)
You still have time to protect your existing conversations before May 8.
Immediate Actions (Before May 8)
- 1Download Your Instagram Data. Go to Settings → Download Your Information. Select "DMs" and other data you want to preserve. Request the download (Instagram typically takes 24-48 hours). Download the file once it's ready. Store safely on your computer or secure cloud storage.
- 2Export Important Conversations. Screenshot or copy text from sensitive conversations. Save them outside of Instagram (Google Docs, encrypted file storage). Especially important for financial, health, or personal information.
- 3Delete Sensitive DMs. Go through old conversations. Permanently delete DMs containing passwords, financial info, or highly personal content. Remember: once May 8 hits, only encryption prevents Meta from accessing deleted messages in their backups.
- 4Switch Sensitive Conversations to Encrypted Apps. For ongoing private communication, move to Signal, Telegram, or similar. Inform your contacts that future sensitive conversations should use these apps. Create a migration plan for important contacts.
Going Forward (May 8+)
1. Use Encrypted Messaging Apps
- Signal (highest privacy standard)
- Telegram (excellent privacy, cloud-based)
- Threema (Swiss-based, no data retention)
2. Enable VPN When Accessing Instagram
- Use VPN to protect your connection metadata when messaging on Instagram
- This prevents your ISP from seeing which accounts you're messaging
- Adds encryption layer between you and Instagram
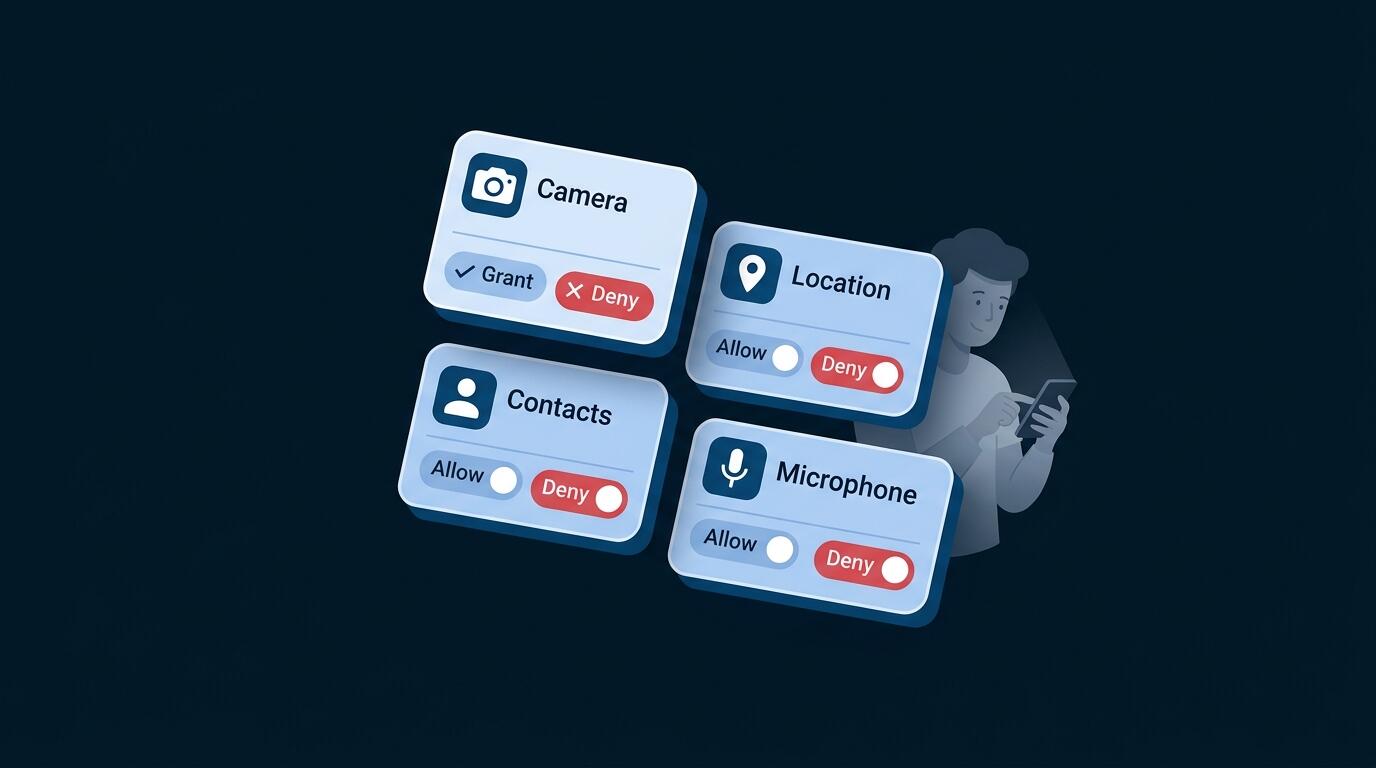
3. Review Instagram Privacy Settings
- Limit who can message you
- Restrict who can see your activity status
- Disable location sharing
- Limit ad targeting permissions
4. Understand What Data Instagram Is Collecting
- Review your ad preferences on Instagram
- See what behavioral categories Meta has assigned to you
- Opt out of behavioral tracking where possible
5. Practice Data Minimization
- Share less personal information on Instagram
- Use separate accounts for professional vs. personal use
- Treat Instagram DMs as semi-public from now on
Move sensitive conversations off Instagram entirely. Signal is free, easy to use, and requires no account—just a phone number. It's the fastest way to add real encryption to your private messages.
Alternatives to Instagram DMs (Privacy Options)
If Instagram DMs are no longer encrypted, what are your alternatives?
Encrypted Messaging Apps
Signal: The gold standard. Military-grade encryption, no metadata collection, completely open-source. Recommended by security experts worldwide.
Telegram: Cloud-based with optional encrypted "Secret Chats." Not as bulletproof as Signal but excellent privacy with better media support.
Threema: Swiss-based, no data retention, pay-once model. Excellent for users who prioritize privacy over convenience.
Why encrypted apps are better: Your message content is mathematically impossible for the provider to access—not just company policy, but technical impossibility.
VPN for Instagram Privacy
VPN protects your connection by encrypting it, but it's not a replacement for encrypted messaging. Here's how VPN helps:
- Protects metadata: Hides your ip address from seeing you're accessing Instagram
- Connection encryption: All data between you and Instagram travels encrypted
- Network privacy: Prevents network monitoring at cafes or public WiFi
- VPN + Instagram: Adds a privacy layer, but Meta can still read message content
Think of it this way: Encryption protects the message. VPN protects the fact that you're sending it.
Email Encryption
For very sensitive conversations, consider encrypted email:
- ProtonMail (end-to-end encrypted email)
- Tutanota (encrypted email and storage)
Email is slower than messaging but appropriate for sensitive, important communication.
Combination Approach (Best Practice)
The strongest privacy strategy layers tools appropriately:
- Casual messages on Instagram: Accept that Meta can read them. Treat Instagram DMs as semi-public.
- Important information: Use encrypted apps (Signal) instead—move conversation off Instagram.
- Public WiFi access: VPN protects your connection on any network, preventing network snooping but not against Meta reading DM content.
- Highly sensitive discussions: Signal + VPN (on public networks) + secure device.
- Critical information: Encrypted email for important records.
Key point: VPN helps with many privacy concerns, but it cannot protect message content from Meta. Only switching to encrypted messaging apps (Signal, Telegram) solves the DM privacy problem.
Frequently Asked Questions
No. Meta will retain them in readable format on their servers. If you had used encrypted DMs, they'll become readable to Meta. This is why downloading them before May 8 is important—it's your only backup of the encrypted version.
For casual conversation, yes. For sensitive information, no. Treat DMs like a semi-public space now.
No. Both WhatsApp and Messenger maintain end-to-end encryption as core features. Meta chose NOT to remove encryption from these platforms, undermining the "simplification" explanation for Instagram's removal. This suggests the decision is specifically about accessing Instagram message data, not about infrastructure burden.
Not the content. But if you don't use VPN, your ISP can see that you're accessing Instagram and which accounts you're messaging.
Not through Instagram. You'll need to use separate encrypted messaging apps.
Facebook Messenger actually made E2EE the default in 2023 and remains encrypted. Instagram is the exception here, not the start of a trend.
For casual social messaging, no. For anything containing passwords, financial info, personal details, or intimate conversations—yes, privacy matters.
Unlikely. Encrypted messaging is their core value proposition. WhatsApp, Signal, and Telegram depend on privacy features to compete with mainstream apps.
No. Signal and Telegram are free. Threema requires a one-time purchase ($3-4).
No. VPN protects your connection and prevents your ISP from seeing you're using Instagram, but it does NOT protect your message content from Meta. Meta can still read every message. For truly private communication, use encrypted messaging apps like Signal instead.